Sunday, March 31, 2013
Careful When You Strip Theres A Secret Video Surveillance Security Camera In There!
Ladies, have you ever felt naughty eyes on you at the stores dressing room? You are probably right. There is someone watching, so better get out.
Thought you were safe from prying eyes?
Each time you shop for a new outfit you always have to check it out in the fitting room. Enclosed in a little space with a mirror, you think you are alone, so you strip and slip on the jeans or dress and strip again to put your clothes back on.
Your intuition must be right to tell that youre on video. Surveillance security camera systems can be used for mischief too and all ladies must beware. Peeping Toms have gone a level higher in their favorite past time. They have tapped the features of a video surveillance security camera and can enjoy viewing the fitting room scenes in the privacy of their home.
Incredible but sadly true
Hidden cameras are a bane and boon to society. It is an emerging menace when the cameras are turned on unsuspecting women who are thinking they are safe in their homes or in public dressing rooms. Unscrupulous persons can make hidden cameras and use remote controls to activate these.
The use of video surveillance security cameras to invade ones privacy is act of terrorism and is against the law. Yet, people misuse these gizmos with impunity. Peeping toms are not the only ones abusing these security systems. Employers can also bully their staff by keeping an overzealous eye on them.
Unless they are caught spying on women in the privacy of dressing rooms, nothing can be done against the culprits. The law, though, has caught up with voyeurs of the Caesars Atlantic City of New Jersey. The gaming palace was fined $80,000 by the Casino Control Commission because of unscrupulous use of video surveillance security cameras.
Spying on the spy
Violators of the laws governing the use of video surveillance security camera equipment face one to five years in prison and penalties, so if you have caught a peeping tom in a public place or even in your neighborhood, you can sue. A tape of the recording must be presented as evidence.
Women must be informed of the ugly side of video surveillance security camera systems meant to protect them. One way to protect yourself from malicious eyes is to have a wireless video camera hunter. This can easily track hidden wireless cameras. When it detects a live wireless video, a signal is displayed immediately on the built-in 2.5" color video screen. The alert tone will sound when it has espied a hidden camera. In this case, it indeed takes a spy to catch a spy.
Informed and alert
Moms should caution their teens about fitting rooms, school washrooms, and public comfort rooms. Ladies should never strip without any cover. Children in day school should also get protection from the improper use of video surveillance security camera systems. Indeed, kids should be taught how to protect themselves and to report suspicious activities. It is always an advantage to be informed and well armed.
Read More..
Thought you were safe from prying eyes?
Each time you shop for a new outfit you always have to check it out in the fitting room. Enclosed in a little space with a mirror, you think you are alone, so you strip and slip on the jeans or dress and strip again to put your clothes back on.
Your intuition must be right to tell that youre on video. Surveillance security camera systems can be used for mischief too and all ladies must beware. Peeping Toms have gone a level higher in their favorite past time. They have tapped the features of a video surveillance security camera and can enjoy viewing the fitting room scenes in the privacy of their home.
Incredible but sadly true
Hidden cameras are a bane and boon to society. It is an emerging menace when the cameras are turned on unsuspecting women who are thinking they are safe in their homes or in public dressing rooms. Unscrupulous persons can make hidden cameras and use remote controls to activate these.
The use of video surveillance security cameras to invade ones privacy is act of terrorism and is against the law. Yet, people misuse these gizmos with impunity. Peeping toms are not the only ones abusing these security systems. Employers can also bully their staff by keeping an overzealous eye on them.
Unless they are caught spying on women in the privacy of dressing rooms, nothing can be done against the culprits. The law, though, has caught up with voyeurs of the Caesars Atlantic City of New Jersey. The gaming palace was fined $80,000 by the Casino Control Commission because of unscrupulous use of video surveillance security cameras.
Spying on the spy
Violators of the laws governing the use of video surveillance security camera equipment face one to five years in prison and penalties, so if you have caught a peeping tom in a public place or even in your neighborhood, you can sue. A tape of the recording must be presented as evidence.
Women must be informed of the ugly side of video surveillance security camera systems meant to protect them. One way to protect yourself from malicious eyes is to have a wireless video camera hunter. This can easily track hidden wireless cameras. When it detects a live wireless video, a signal is displayed immediately on the built-in 2.5" color video screen. The alert tone will sound when it has espied a hidden camera. In this case, it indeed takes a spy to catch a spy.
Informed and alert
Moms should caution their teens about fitting rooms, school washrooms, and public comfort rooms. Ladies should never strip without any cover. Children in day school should also get protection from the improper use of video surveillance security camera systems. Indeed, kids should be taught how to protect themselves and to report suspicious activities. It is always an advantage to be informed and well armed.
Microsoft Word tutorial for Windows XP
Go to the Start Button on the Desktop and press it. Click on All Programs. 2. Click on Microsoft Office, then Microsoft Office Word 2007. 3. This opens the Word 2007 program.The MENU bar is displayed below. If you need to see more options for that specific menu (i.e. font) click on the downward arrow at the bottom, as shown below. In previous versions of WORD, the toolbars were modifiable by selecting a drop-down menu under the VIEW menu option. In 2007 WORD, all toolbars are displayed when you select that menu option. A new feature of WORD 2007 is the Quick Access Toolbar, which can be displayed above or below the ribbon (as displayed below the ribbon, above). 2. To customize this feature, RIGHT click on the Ribbon, and select CUSTOMIZE QUICK ACCESS TOOLBAR. (Displayed below). If you need to open this document on a computer that runs a previous version of Microsoft Office (1997, XP, 2003, etc.), you MUST save this file in a previous version.
Read More..
Get from here to download Microsoft Word tutorial for Windows XP
Cisco Catalyst 6500 Series Switch Data Sheet
The Catalyst 6500 Series sets the new standard for IP communications and application delivery in enterprise campus and service provider networks by maximizing user productivity and enhancing operational control while providing unprecedented investment protection. As Cisco’s premier intelligent multilayer modular switch, the Catalyst® 6500 Series delivers secure, converged services, end-to-end, from the wiring closet to the core, to the data center, to the WAN edge.
Ideal for enterprises and service providers seeking to reduce their total cost of ownership, the Cisco Catalyst 6500 Series delivers scalable performance and port density across a range of chassis configurations and LAN/WAN/MAN interfaces. Available in 3-, 6-, 9-, and 13-slot chassis, Cisco Catalyst 6500 Series switches feature an unparalleled range of integrated services modules, including multigigabit network security, content switching, telephony, and network analysis modules.
By taking advantage of a forward-thinking architecture that uses a common set of modules and operating system software across all Cisco Catalyst 6500 Series chassis, the Catalyst 6500 Series delivers a high level of operational consistency that optimizes IT infrastructure usage and enhances return on investment. From 48-port to 576-port 10/100/1000 Ethernet wiring closets to hundreds-of-Mpps network cores supporting up to 192 1-Gbps or 32 10-Gbps trunks, the Cisco Catalyst 6500 Series provides an optimal platform that maximizes network uptime with stateful failover capability between redundant routing and forwarding engines.
download Cisco Catalyst 6500 Series Switch Data Sheet
Read More..
Ideal for enterprises and service providers seeking to reduce their total cost of ownership, the Cisco Catalyst 6500 Series delivers scalable performance and port density across a range of chassis configurations and LAN/WAN/MAN interfaces. Available in 3-, 6-, 9-, and 13-slot chassis, Cisco Catalyst 6500 Series switches feature an unparalleled range of integrated services modules, including multigigabit network security, content switching, telephony, and network analysis modules.
By taking advantage of a forward-thinking architecture that uses a common set of modules and operating system software across all Cisco Catalyst 6500 Series chassis, the Catalyst 6500 Series delivers a high level of operational consistency that optimizes IT infrastructure usage and enhances return on investment. From 48-port to 576-port 10/100/1000 Ethernet wiring closets to hundreds-of-Mpps network cores supporting up to 192 1-Gbps or 32 10-Gbps trunks, the Cisco Catalyst 6500 Series provides an optimal platform that maximizes network uptime with stateful failover capability between redundant routing and forwarding engines.
download Cisco Catalyst 6500 Series Switch Data Sheet
Conference Calls Control Time And Space Not Minds
I always associate corporate culture with suits and ties in high summer, and with unending business meetings. I always picture these meetings being held in an air-conditioned conference room with a long rectangular table where the delegates are seated, some attentive, others bored, yet others thinking about the lunch hour. One person or two people at a time stand up to give a presentation, complete with graphs, charts, and statistics. Thereafter, there are questions, debates, arguments, and sometimes a conclusion. Finally, everyone files out towards the cafeteria.
Of course, these days, it is no longer necessary to have those really long tables at a conference room, thanks to the development of methods like conference calls and web conferencing. These are used increasingly frequently by corporate organizations to overcome the hurdles put up by time and space.
These days organizations that offer services to facilitate conference calls have been becoming increasingly competitive. And why shouldnt they? As demand for conferencing rises, so too will the supply, and everybody wants to prove that they are the best. So each conference call service provider tries to provide better service. So you can get CDs recording all that took place in the discussion. Also, the person hosting the conference call usually has access to a number of features that may be used to better the conference.
Perhaps I am being old-fashioned when I say that nothing can replace the good old days when every conference delegate was within touching distance. I am not convinced that the personal touch element can be achieved through conference calls. Can a conference call really be a good enough substitute?
Then again, conferencing is quite a cost effective way of getting ones employees together. The organization no longer has to spend as much on travel expenses to get people from far and wide to attend a meeting at a tiny portion of the globe. All it takes is a little expense on the technology involved, a little planning, and a conference call can be conducted with great ease. With a little practice, even those that are not what one might call technologically savvy, will soon be successfully having meetings with people who are continents away.
However, as with the meetings prior to conference calls, one can never really count on having everyones mind on the job. That more than one mind will be wandering elsewhere, is guaranteed. Even with all our progress, the development of humanoid robots, cloned sheep and so on, we have yet to learn how to go about controlling peoples minds.
Read More..
Of course, these days, it is no longer necessary to have those really long tables at a conference room, thanks to the development of methods like conference calls and web conferencing. These are used increasingly frequently by corporate organizations to overcome the hurdles put up by time and space.
These days organizations that offer services to facilitate conference calls have been becoming increasingly competitive. And why shouldnt they? As demand for conferencing rises, so too will the supply, and everybody wants to prove that they are the best. So each conference call service provider tries to provide better service. So you can get CDs recording all that took place in the discussion. Also, the person hosting the conference call usually has access to a number of features that may be used to better the conference.
Perhaps I am being old-fashioned when I say that nothing can replace the good old days when every conference delegate was within touching distance. I am not convinced that the personal touch element can be achieved through conference calls. Can a conference call really be a good enough substitute?
Then again, conferencing is quite a cost effective way of getting ones employees together. The organization no longer has to spend as much on travel expenses to get people from far and wide to attend a meeting at a tiny portion of the globe. All it takes is a little expense on the technology involved, a little planning, and a conference call can be conducted with great ease. With a little practice, even those that are not what one might call technologically savvy, will soon be successfully having meetings with people who are continents away.
However, as with the meetings prior to conference calls, one can never really count on having everyones mind on the job. That more than one mind will be wandering elsewhere, is guaranteed. Even with all our progress, the development of humanoid robots, cloned sheep and so on, we have yet to learn how to go about controlling peoples minds.
Microsoft Word tutorial for Windows XP
Microsoft Word tutorial for Windows XP - Welcome to our blog and we hope you will enjoy it very much. Guys, what are you looking for is here. You can also download it below. Go to the Start Button on the Desktop and press it. Click on All Programs. 2. Click on Microsoft Office, then Microsoft Office Word 2007. 3. This opens the Word 2007 program.The MENU bar is displayed below. If you need to see more options for that specific menu (i.e. font) click on the downward arrow at the bottom, as shown below.
In previous versions of WORD, the toolbars were modifiable by selecting a drop-down menu under the VIEW menu option. In 2007 WORD, all toolbars are displayed when you select that menu option. A new feature of WORD 2007 is the Quick Access Toolbar, which can be displayed above or below the ribbon (as displayed below the ribbon, above). 2. To customize this feature, RIGHT click on the Ribbon, and select CUSTOMIZE QUICK ACCESS TOOLBAR. (Displayed below). If you need to open this document on a computer that runs a previous version of Microsoft Office (1997, XP, 2003, etc.), you MUST save this file in a previous version.
In previous versions of WORD, the toolbars were modifiable by selecting a drop-down menu under the VIEW menu option. In 2007 WORD, all toolbars are displayed when you select that menu option. A new feature of WORD 2007 is the Quick Access Toolbar, which can be displayed above or below the ribbon (as displayed below the ribbon, above). 2. To customize this feature, RIGHT click on the Ribbon, and select CUSTOMIZE QUICK ACCESS TOOLBAR. (Displayed below). If you need to open this document on a computer that runs a previous version of Microsoft Office (1997, XP, 2003, etc.), you MUST save this file in a previous version.
download Microsoft Word tutorial for Windows XP
How To Import LinkedIn Contacts To Gmail
Your LinkedIn profile is a valuable asset for your professional career, it helps you find and connect with like minded people who are on the same career path as yours. Overtime, as you switch employers and companies, your LinkedIn address book grows and you have a good list of friends and professionals whom you would not want to lose.
There is a strong reason why I would suggest you to backup and export contacts from LinkedIn, Facebook and other social media accounts and import them in your email account. Let’s say you are friends with a very good contact who is a recruiting manager in one of your dream companies. You interact with this person often, send him personal messages, comment on his updates and interact quite often. You do not know his email address but you are just friends with him on LinkedIn.
After a few months, you see that the contact is missing from your LinkedIn profile. As it turns out, either the person has deleted you from his network or he has shut down his LinkedIn account which means now there is no way you can contact this person or send him an email. However, if you had a backup file containing the email addresses or phone numbers of all your LinkedIn friends, you still have the chance of contacting this person.
Export LinkedIn Contacts As A CSV FIle
Unfortunately, LinkedIn has no easy way to migrate contacts from LinkedIn to Gmail directly from the web. You have to export all your LinkedIn contacts as a CSV file and then import the whole list into your Gmail account or Google contacts.Here is how to backup LinkedIn contacts and export the backup as a CSV file, which can be used later on:
1. Login to your LinkedIn account and go to the “Contacts” page.

2. Clicking the small “Select all” option will select all your LinkedIn contacts.Once that is done, scroll down and click “Export connections” at the bottom of the page.

This is important. If you want to export the contact details of selected LinkedIn friends, you can do so by removing contacts from the right sidebar. There are different options to sort LinkeIn contacts by companies and connections, so you can filter by company name and export LinkedIn contacts from a specific company or employer.
3. In the next page, choose “Export to Microsoft Outlook (.csv)” and hit the “Export” button. This will export all your LinkedIn contacts into a CSV file, which you can save in your computer’s hard drive.

Import LinkedIn Contacts To Gmail
Now that you have successfully downloaded a backup of all your LinkedIn contacts, it’s time to import the whole contacts list in your Gmail account. Before you import LinkedIn contacts to your Google account, here are a few things you should knowFirst, the backup file will have the following fields for all contacts that are connected to you on LinkedIn
- Job title
- First Name
- Middle Name
- Last Name
- E-mail Address
- Address
- City
- State
- Postal Code
- Country
- Company
- Website
Now back to importing a CSV list of LinkedIn contacts in your Gmail or Google account:
1. Login to your Gmail account, and click the “Gmail” drop-down right below the Google logo. Next, choose “Contacts”

2. Next, click “Import contacts” from the left sidebar and then choose the csv file which you exported from your LinkedIn account.

3. Hit “Import” and you have successfully transferred email addresses of all your LinkedIn friends and contacts to your Google account.
The only problem with this approach is of course it is manual and you have to do it time and again to ensure that all your LinkedIn contacts and Gmail contacts are in sync. For example, once in every 6 months, I clean up unnecessary friends from my social media accounts (Facebook, Twitter, Google Plus, LinkedIn) and merge contacts from all my social accounts into Gmail. I do this because I don’t want to lose a contact, if the person decides to shut down his LinkedIn account or Facebook account for some reason.
Via Ampercent
Saturday, March 30, 2013
ATT Sony Xperia Z price ads

With ATT Sony Xperia Z price ads, the Sony device will cost as much as ATT
iPhone. Related to ATT Sony Xperia Z specs leaked with a 5-inch 1080p quad-core
1.5GHz Snapdragon S4 Pro processor from Qualcomm. It will also be likely to
have 2GB of RAM and a 13MP rear-facing camera, this device will competition
with
HTC DROID DNA
Microsoft Outlook 2007 Tutorial
Finally, perhaps the most important Menu is the Help item, as you can open Help and select “Microsoft Office Outlook Help and search the Microsoft Outlook site for instructions, procedures, problem resolutions, etc.To create a new distribution list, open the File menu and select New and then Distribution List (or from inside Outlook 2007, press Ctrl+Shift+L):To see the new entry, open Outlook 2007, Select New, then To. When the Global Address list appears, open the drop down list under Address Book and select Contacts.Similar to having an assistant help you manage your incoming paper mail, you can useMicrosoft Outlook 2007 to allow another person, known as a delegate, to receive and respond to meeting requests or responses and to send e-mail messages on your behalf. now the manual grant additional permissions that allow your delegate to read, create, or have full control over items in your Exchange mailbox. Delegate Access is most commonly used between a manager and his or her assistant, where the assistant (delegate) is responsible for processing the manager’s incoming meeting requests or e-mail messages and coordinating the manager’s schedule. When a delegate has Send on Behalf permissions, the delegate can compose an e-mail message and enter the manager’s name in the From box. Recipients of the e-mail message will see the text Delegate Name on behalf of Manager Name next to From.
Click here to Download Microsoft Outlook 2007 Tutorial
Cobook is a Simpler and Better Replacement for iPhone Contacts App
Cobook is a Simpler and Better Replacement for iPhone Contacts App:
 One of my greatest gripes with the iPhone, iPad and iPod Touch, is how little Apple’s set of native apps have evolved over time. There are exceptions to this of course, like Mail, Photos and Safari, which have changed and improved to some degree, but overall, most of the core Apple set of native apps have remained the same.
One of my greatest gripes with the iPhone, iPad and iPod Touch, is how little Apple’s set of native apps have evolved over time. There are exceptions to this of course, like Mail, Photos and Safari, which have changed and improved to some degree, but overall, most of the core Apple set of native apps have remained the same.
One of the most glaring examples of this is Apple’s Contacts app, which besides some basic changes in its looks, has basically remained unaltered through the entire existence of Apple’s smartphone since it debuted in the market on 2007. Because of that, there has been a flood of contact applications that have showed up on the App Store, but due to the vast amount of these available, it is not easy to choose the best one.
Of course, every user has their own needs and tastes, but of all the free contacts apps that’s I’ve tried, Cobook has proved to be the best one so far. Let’s take a look at what makes it a great choice for anyone looking to replace the native iPhone Contacts app.

To start, the app allows you to choose from among only your iPhone contacts or from all of them, including the ones you create on the app itself. This might sound redundant, but it takes us to a very important feature of Cobook: The app does not integrate with any online service and instead keeps your contacts stored locally. Some people like to have their all their contacts and calendar data stored on the cloud, but for those who don’t and who like to keep their sensitive contact information private, Cobook is a great alternative.


As mentioned above, Cobook allows you to access your contacts in different ways. Upon opening the app you can immediately access your contact list, which you can search in the traditional way using the search field at the top of the screen. In addition to that though, tapping the grid icon at the next to the search option at the bottom of the screen will take you to a sort of dial pad where you can search through your contacts either by name or phone number.


I found this search method very efficient and is the one I use the most.


You can, for example, add your Twitter account and can start navigating through it and adding contacts to Cobook right from your Twitter profile. Cobook pulls all the necessary information from each Twitter contact or Facebook friend and gets it ready for you to add to the app.


If at some point you want to filter out all those contacts you added from your social networks, you can use the All Contacts/iPhone Contacts option mentioned above to do so.
Via Guidingtech

Cobook is a Simpler and Better Replacement for iPhone Contacts App
- Tweet
 One of my greatest gripes with the iPhone, iPad and iPod Touch, is how little Apple’s set of native apps have evolved over time. There are exceptions to this of course, like Mail, Photos and Safari, which have changed and improved to some degree, but overall, most of the core Apple set of native apps have remained the same.
One of my greatest gripes with the iPhone, iPad and iPod Touch, is how little Apple’s set of native apps have evolved over time. There are exceptions to this of course, like Mail, Photos and Safari, which have changed and improved to some degree, but overall, most of the core Apple set of native apps have remained the same.One of the most glaring examples of this is Apple’s Contacts app, which besides some basic changes in its looks, has basically remained unaltered through the entire existence of Apple’s smartphone since it debuted in the market on 2007. Because of that, there has been a flood of contact applications that have showed up on the App Store, but due to the vast amount of these available, it is not easy to choose the best one.
Of course, every user has their own needs and tastes, but of all the free contacts apps that’s I’ve tried, Cobook has proved to be the best one so far. Let’s take a look at what makes it a great choice for anyone looking to replace the native iPhone Contacts app.
A Better Contacts App
Many apps out there are usually judged by the number of options and features they have, yet in the case of contacts apps, the simpler and more functional they are, the better. This is exactly what Cobook achieves, with a simple interface and different ways to access your contacts.
To start, the app allows you to choose from among only your iPhone contacts or from all of them, including the ones you create on the app itself. This might sound redundant, but it takes us to a very important feature of Cobook: The app does not integrate with any online service and instead keeps your contacts stored locally. Some people like to have their all their contacts and calendar data stored on the cloud, but for those who don’t and who like to keep their sensitive contact information private, Cobook is a great alternative.


As mentioned above, Cobook allows you to access your contacts in different ways. Upon opening the app you can immediately access your contact list, which you can search in the traditional way using the search field at the top of the screen. In addition to that though, tapping the grid icon at the next to the search option at the bottom of the screen will take you to a sort of dial pad where you can search through your contacts either by name or phone number.


I found this search method very efficient and is the one I use the most.
Additional Features
One of the best features of Cobook in my opinion is the way it integrates with social networks like Facebook, Twitter and LinkedIn.

You can, for example, add your Twitter account and can start navigating through it and adding contacts to Cobook right from your Twitter profile. Cobook pulls all the necessary information from each Twitter contact or Facebook friend and gets it ready for you to add to the app.


If at some point you want to filter out all those contacts you added from your social networks, you can use the All Contacts/iPhone Contacts option mentioned above to do so.
Final Thoughts on Cobook
As you have seen, Cobook brings to the table a few tricks that put the native Contacts app to shame, and does so while at the same time remaining simple and easy to use. Give it a try and let us know if it has enough to become your default contacts app.Via Guidingtech
Nokia Lumia 920 For ATT Price Drops To $69.99
Nokia Lumia 920 For ATT
Price Drops To $69.99 On Amazon – Nokia Lumia 920 for ATT now has offers with
more cheap on Amazon comparing with the carrier offers on its store. ATT Nokia
Lumia 920 has received a discount on Amazon Wireless for only $69.99 with two
year agreement.
Link Load Balancing Take a Load Off Annie
Link Load Balancing evens out critical resources on data networks with unpredictable requests issued to a server. For example, a web site with heavy traffic may employ two, three or more servers in a link load balancing program. The link load balancing routines enable a network to "juggle" more traffic that otherwise possible If one server is overwhelmed, the link load balancing scheme forwards them to a different server with extra capacity.
Another aspect to link load balancing concerns the communications channels themselves. In this case the "juggling act" is meant to better distribute processing and communications demands more equitably across the network so that no single a computer is overwhelmed by the demand.
Link Load Balancing - Key Features & Benefits
First and foremost is "availability" - 24/7 Application Availability for complete IP Application access. Local and Global Service providers rely on redundancy and link load balancing between servers, WSD units and distributed sites for complete server continuity across global networks
Network Bottlenecks - Link Load Balancing
Network managers are constantly seeking new solutions for eliminating bottlenecks and latencies for the fastest performance of all networked applications and web-enabled transactions. The idea link load balancing technology combines both unlimited application scalability with flexible traffic distribution management of data centers and server farms.
Network Security - Link Load Balancing
Link load balancing is a key element in the overall network Intrusion Prevention effort. Expert Link Load Balancing guards the network against internal and external attacks such as viruses, worms, Trojans, anti-scanning and protocol anomalies. Above all hovers the ultimate link load balancing challenge and network threat – DOS - Denial of Service.
Remember the song, "Take a load off Annie" Just listening to it makes you feel nice and relaxed… For maximum performance and 100 percent uptime, networks use link load balancing to even out resource use throughout the network.
Read More..
Another aspect to link load balancing concerns the communications channels themselves. In this case the "juggling act" is meant to better distribute processing and communications demands more equitably across the network so that no single a computer is overwhelmed by the demand.
Link Load Balancing - Key Features & Benefits
First and foremost is "availability" - 24/7 Application Availability for complete IP Application access. Local and Global Service providers rely on redundancy and link load balancing between servers, WSD units and distributed sites for complete server continuity across global networks
Network Bottlenecks - Link Load Balancing
Network managers are constantly seeking new solutions for eliminating bottlenecks and latencies for the fastest performance of all networked applications and web-enabled transactions. The idea link load balancing technology combines both unlimited application scalability with flexible traffic distribution management of data centers and server farms.
Network Security - Link Load Balancing
Link load balancing is a key element in the overall network Intrusion Prevention effort. Expert Link Load Balancing guards the network against internal and external attacks such as viruses, worms, Trojans, anti-scanning and protocol anomalies. Above all hovers the ultimate link load balancing challenge and network threat – DOS - Denial of Service.
Remember the song, "Take a load off Annie" Just listening to it makes you feel nice and relaxed… For maximum performance and 100 percent uptime, networks use link load balancing to even out resource use throughout the network.
Friday, March 29, 2013
Importing Editing and Compressing Video in iMovie 06 Tutorial
Importing/Editing and Compressing Video in iMovie 06 Tutorial.You’ll notice that iMovie has created a new clip in the clips pane to the right of the iMovie monitor whenever the camera was stopped or paused during filming.Click Create. iMovie should open your project in Camera Mode and display the message Camera Connected , but if No Camera Connected displays instead, make sure that the camera is connected properly, turned on, and in Playback Mode. Click Import. Please note that your footage will upload in real time . In other words, if your footage is thirty minutes long, it will take thirty minutes to upload. You cannot begin editing until the movie has uploaded completely. The default location of both the playhead and crop markers is at the far left of the blue line beneath the iMovie monitor. The playhead can be moved to a specific time to view playback from that time on, while the crop markers can be used to edit your clips.
Download: Importing/Editing and Compressing Video in iMovie 06 Tutorial
Read More..
Download: Importing/Editing and Compressing Video in iMovie 06 Tutorial
Microsoft Word Mail Merge Tutorial
you generate form letters also lets you easily create mailing labels.To do this, download on Tools, then Letters and Mailings, then select the Mail Merge Wizard. There are pre-cut mailing labels available, and it is easy to configure the mailing labels to fit the size of your label. Click on Label options.Select the kind of printer you will be using to print the mailing labels, and then select the brand of your label.When you have selected a brand, it will show the different models available for the brand. The details of each label will be shown. It is important to select the correct label as each label come in different sizes.You can use an existing list from a previous mail merge session or from an Excel file, pick recipients from your Outlook contacts or type a new list. In this example, we will use an Excel spreadsheet. Click on Browse to select the Excel file to use as a data source.
Click here to Download Microsoft Word Mail Merge Tutorial
Getting started with SQL Developer Tutorial
Getting started with SQL Developer Tutorial. How to get going, from the ground up… Making use of Free OS, database and development tools. What is SQL Developer ? How can I get it ? Pointers to installing Centos Linux and Oracle XE Brief install details Java Development Kit Installing SQL Developer Connecting to database Create and populate application tables Basic usage for SQL and PL/SQL development DBA related tasks. HTML based tutorial Starting SQL Developer Establish database connection Create a simple table Enter data manually Query data using SQL Import data from spreadsheet file (Oracle XE web GUI) Create and run a simple PL/SQL procedure. DBA usage of SQL Developer.
Download: Getting started with SQL Developer Tutorial
Read More..
Download: Getting started with SQL Developer Tutorial
Set Your iPhone’s Screen To Turn Off Automatically When In Your Pocket
Set Your iPhone’s Screen To Turn Off Automatically When In Your Pocket:

The iPhone is called a smartphone because it is meant to stay apprised of your needs and surroundings in order to automatically optimize usage to the maximum possible extent. You might have installed a lot of luxury apps on your device, but at times, it’s the little things make the most difference in daily usage. One such feature is the iPhone’s ability to turn off its display whenever you hold it to your ear during a call. This behavior is controlled by the proximity sensor located at the front of your device. There might not seem to be too many uses of this sensor by default, but no part of an iDevice escapes the notice of the crafty developers working to keep the Cydia store populated. Always On Proximity is a new tweak that puts the proximity sensor in your iPhone to good use. With this tweak installed, you can quickly enable or disable the sensor from anywhere within the OS using an Activator gesture, causing the device to respond to it and power off the screen when, say, you put the device in your pocket.


The tweak might not make sense at first, but there are a lot of scenarios where Always On Proximity can come in handy. Before we discuss any of the usage scenarios though, let’s first find out what exactly Always On Proximity does. The tweak works with Activator, but this does not mean that your screen will go blank as soon as the assigned gesture is performed. The gesture only brings the proximity sensor to an active state. You will get a notification every time the tweak is toggled.
When Always On Proximity is enabled, the screen goes blank as soon as the proximity sensor is covered by an object. Now, you might be wondering what purpose this could possibly serve. Well, the tweak is mostly meant to add a bit of convenience to the way you interact with your device before and after putting it away for a while. Usually, you would hit the power button to lock the device before putting it on your desk or back into your pocket because you’d want to save precious minutes of battery life. With this tweak installed, all you have to do is place it face down on the desk or simply put it in your pocket without touching the power button. The proximity sensor will automatically power the screen off for you, making those long email and messaging conversations much less taxing.
It might also come in handy if you have a lock screen passcode, don’t want to have to enter it again and again while you’re at home and would prefer not to disable it entirely.
We can’t say that everyone is going to like Always On Proximity, but if you usually find the need to check your iDevices several times every few minutes, you should definitely give it a try. It is available for free in Cydia’s BigBoss repo.
Advertisement


The tweak might not make sense at first, but there are a lot of scenarios where Always On Proximity can come in handy. Before we discuss any of the usage scenarios though, let’s first find out what exactly Always On Proximity does. The tweak works with Activator, but this does not mean that your screen will go blank as soon as the assigned gesture is performed. The gesture only brings the proximity sensor to an active state. You will get a notification every time the tweak is toggled.
When Always On Proximity is enabled, the screen goes blank as soon as the proximity sensor is covered by an object. Now, you might be wondering what purpose this could possibly serve. Well, the tweak is mostly meant to add a bit of convenience to the way you interact with your device before and after putting it away for a while. Usually, you would hit the power button to lock the device before putting it on your desk or back into your pocket because you’d want to save precious minutes of battery life. With this tweak installed, all you have to do is place it face down on the desk or simply put it in your pocket without touching the power button. The proximity sensor will automatically power the screen off for you, making those long email and messaging conversations much less taxing.
It might also come in handy if you have a lock screen passcode, don’t want to have to enter it again and again while you’re at home and would prefer not to disable it entirely.
We can’t say that everyone is going to like Always On Proximity, but if you usually find the need to check your iDevices several times every few minutes, you should definitely give it a try. It is available for free in Cydia’s BigBoss repo.
Advertisement
Microsoft Access 2007 Tutorial
Microsoft Office Access 2007 Or MS access 2007 organizes your information into tables: lists of rows and columns reminiscent of an accountant’s pad or a Microsoft Office Excel 2007 worksheet. In a simple database, you might have only one table. For most databases you will need more than one. For example, you might have a table that stores information about products, another table that stores information about orders, and another table with information about customers. What is a table? A table contains data about a particular subject, such as employees or products. Each record in a table contains information about one item, such as a particular employee. Each row is also called a record , and each column, is also called a field . A record is a meaningful and consistent way to combine information about something. A field is a single item of information — an item type that appears in every record . In the Products table, for instance, each row or record would hold information about one product. Each column or field holds some type of information about that product, such as its name or price. A record is made up of fields , such as name, address and telephone number…
Click here to Download Microsoft Access 2007 Tutorial
Quick Microsoft Access 2003 Tutorial
This tutorial is intended for computer science students who need a quick introduction to Microsoft Access, but it will be useful to anyone needing such an introduction. To get the full benefit of this tutorial, you will need a computer running one of Microsoft Windows 95 or higher, Microsoft NT 4.0 or higher, or Microsoft Windows 2000/XP. You will also need to have a copy of Microsoft Access 2003 installed. 2 First, a few words about what Microsoft Access 2003 is and isn’t. People who don’t really understand what a relational database system is, and some people who don’t actually understand what Access 2003 is, will tell you that Microsoft Access is not a fully relationaldatabase system. In the database world, not being fully relational is very bad. Don’t worry, the people who tell you that are like the people who try to tell you that linux is not a 32 bit operating system. Access 2003, and its predecessors Access 95, 97 and 02, are excellent fully relationaldatabase systems.
Thursday, March 28, 2013
MICROSOFT WORD 2007 TUTORIAL
This is the Quick Access Toolbar and how to know more about MICROSOFT WORD 2007 . With this tool bar one can set it up to fit his/her needs. To do so just click the arrow at the end of this bar and select which items best suit your needs. They will be placed in the order they are selected. Again to customize this Quick Access Toolbar go to the office button and select Word Options. Click customize on the left and you can search for any buttons that suit your needs. A Shortcut to customize this bar is to right click in the Tabs bar and select Customize Quick Access Toolbar. 3. This is the Tabs Bar . Tabs are similar to the menu system of MW2003 instead of having dropdown menus MW2007 created the Tab and Ribbon system. When you select a tab it will display the Ribbon associated with that tab. Here everything has been changed into button form.
Oracle MySQL Cluster Owner Manual Tutorial
Oracle MySQL Cluster Owner Manual Tutorial. This document is a handout for the Oracle MySQL Cluster Tutorial. Please also check the slides which were shown turing the tutorial.MySQL Cluster is a tool which could help make your data Highly Available. This tutorial will help you run a MySQL Cluster, show how to manage it and discuss various topics such as performance, backups and schema considerations. Before going any further we need to setup the Virtual Machine (VM) running under VirtualBox. You can install MySQL Cluster yourself following instructions found in section Installation and Configuration, but we strongly suggest to stick to the filesystem layout and configuration files (found on the DVD).Andrew Hutchings is a MySQL Support Engineer for Oracle Corporation specialising in MySQL Cluster and C/C++ APIs. He is based in the United Kingdom and has worked for MySQL/Sun since 2008. Before joining Sun he was the Technical Architect, Senior Developer and DBA for a major UK magazine publisher. In his spare time Andrew develops various bug fixes and features for MySQL and MySQL Cluster.
Download: Oracle MySQL Cluster Owner Manual Tutorial
Read More..
Download: Oracle MySQL Cluster Owner Manual Tutorial
Add ‘Keep On Top’ Other Handy Options To Application Window Menu
Add ‘Keep On Top’ & Other Handy Options To Application Window Menu:

Read More..
In the past, we have covered several tiny Windows utilities that help you with your workflow by providing quick access to certain actions. For instance, Peek Through allows you to make any window transparent and even click elements of the underlying window through it, and Volumouse lets you control several system components using the mouse wheel. Applications like these give you greater control over your system without interfering with its normal functionality. WindowMenuPlus is another similar tool that adds a set of options to the right-click context menu of every window. These extended options allow you to keep the window on top, move or maximize it to a particular area of the screen, change its transparency, kill its process, view extended information about the program, change the process priority, and minimize the window to system tray. Keep reading to find out more about WindowMenuPlus
During installation, make sure that you uncheck the installation of SweetPacks to avoid getting unwanted software on your computer.

Even though the application’s description says that it works on every window, it did not work for internet browsers including Chrome, Firefox and Internet Explorer in our testing. Otherwise, it seemed to be working on windows of all system tools as well as third party applications. After installation, it runs in the system tray and right-clicking its icon allows you to enable or disable it, change the language and select the components to show in the menu.

You can right-click the title bar of any program window to view the extended options. As mentioned above, these options allow you to keep the window on top, maximize it, move it to any part of the desktop, position and resize to one of several handy preset positions including vertically full, horizontally full, left, right, top, bottom, left-top, right-top, left-bottom and right-bottom.

You can change the window transparency to any level from 0% – 90% with intervals of 10%.

The app also lets you kill processes, take a quick glance at your computer’s available free memory, and change the process priority without having to open the Task Manager.

Moreover, you can instantly locate the parent directory of an application by clicking Find this Program, and view detailed program information of each open application window.

WindowMenuPlus works on both 32-bit and 64-bit versions of Windows XP, Windows Vista, Windows 7 and Windows 8.
Download WindowMenuPlus
During installation, make sure that you uncheck the installation of SweetPacks to avoid getting unwanted software on your computer.

Even though the application’s description says that it works on every window, it did not work for internet browsers including Chrome, Firefox and Internet Explorer in our testing. Otherwise, it seemed to be working on windows of all system tools as well as third party applications. After installation, it runs in the system tray and right-clicking its icon allows you to enable or disable it, change the language and select the components to show in the menu.

You can right-click the title bar of any program window to view the extended options. As mentioned above, these options allow you to keep the window on top, maximize it, move it to any part of the desktop, position and resize to one of several handy preset positions including vertically full, horizontally full, left, right, top, bottom, left-top, right-top, left-bottom and right-bottom.

You can change the window transparency to any level from 0% – 90% with intervals of 10%.

The app also lets you kill processes, take a quick glance at your computer’s available free memory, and change the process priority without having to open the Task Manager.

Moreover, you can instantly locate the parent directory of an application by clicking Find this Program, and view detailed program information of each open application window.

WindowMenuPlus works on both 32-bit and 64-bit versions of Windows XP, Windows Vista, Windows 7 and Windows 8.
Download WindowMenuPlus
How to Import Data into Microsoft Access
Working with data in Microsoft Access databases can be preferable to working with spreadsheets for a number of reasons. One database file can hold several tables, which makes consolidating and organizing data easier. Databases are also great for calculating summaries and aggregating data more efficiently than a spreadsheet. Access is a relational database, which means that you can bring related data stored in different tables together to summarize and calculate data; a feat that a spreadsheet like Excel cannot perform.Databases are a necessity when working with large datasets, as spreadsheets have a limit of 65,000 records. Finally, Microsoft Access databases are compatible with ArcGIS, as tables within Access databases can be directly accessed by ArcGIS and added to ArcMap. Tables can then be joined to boundary files based on a common field, and the data within the tables can be mapped. This is highly preferable to working with table in the dbf file format, which has very particular syntax rules that makes them difficult to work with. Accessdatabases can also serve as geodatabases for holding boundary files and data tables (for instructions on importing shapefiles into Access, see the Import Shapefiles to Access tutorial).
Is DVD replication better than DVD duplication
This is probably the no. 1 most frequently asked question that we get. Many people think that they are the same and use these 2 words interchangeably. Some people say one but actually mean the other. It creates a lot of confusion because each method has its pros and cons. If you are trying to get a price and time estimate even at the same quantity you might get wildly different answers.
DVD Duplication
DVD duplication (a.k.a burned DVD) is the process to create the content using DVD-R media. In other words, a duplicator is used to create or "burn" the source image to another pre-manufactured DVD-R.
DVD Replication
DVD replication (a.k.a pressed DVD) creates a glass master from a pre-mastered image. Stampers are subsequently created from glass master. The stampers will then be used to press the discs with injection molding made of raw polycarbonate plastic.
Whats the big deal?
Now you might be asking, "So whats the big deal? So they are different process". A big deal if you ask me. Replication is the de facto process for higher quantity manufacturing, say 1000 pieces and up. With replication, there is usually a setup cost because stampers and films that need to be made. A longer production time is also expected, most stampers need the entire day to make. We get a lot of wows when clients hear about how long it takes to replicate discs, the truth is, it is a much more complicated process that requires careful quality control and monitoring. The more you make, the cheaper it is with replication.
Lower quantities (we call it short-runs) are mostly done with duplication. With this method the setup is much quicker, since all we will be using is a duplication tower. It is also more economical because of little to none setup cost. That is why companies are able to have a very low minimum (such as 10 or 50) with duplication. You will get your products much quicker, usually within a few days time, but you do pay a higher per unit price for each disc.
Is duplication lower quality than replication?
The short answer is no. The quality of the products is only as good as the original master. What most people are concerned with is the compatibility of discs with DVD players. It is not the same as quality. Nowadays about 90-95% of players are compatible with CD-R/DVD-R, with the exception of Playstation and X-Box. Just remember, the key is to thoroughly test the original master, otherwise problems will still arise no matter which method you use.
Read More..
DVD Duplication
DVD duplication (a.k.a burned DVD) is the process to create the content using DVD-R media. In other words, a duplicator is used to create or "burn" the source image to another pre-manufactured DVD-R.
DVD Replication
DVD replication (a.k.a pressed DVD) creates a glass master from a pre-mastered image. Stampers are subsequently created from glass master. The stampers will then be used to press the discs with injection molding made of raw polycarbonate plastic.
Whats the big deal?
Now you might be asking, "So whats the big deal? So they are different process". A big deal if you ask me. Replication is the de facto process for higher quantity manufacturing, say 1000 pieces and up. With replication, there is usually a setup cost because stampers and films that need to be made. A longer production time is also expected, most stampers need the entire day to make. We get a lot of wows when clients hear about how long it takes to replicate discs, the truth is, it is a much more complicated process that requires careful quality control and monitoring. The more you make, the cheaper it is with replication.
Lower quantities (we call it short-runs) are mostly done with duplication. With this method the setup is much quicker, since all we will be using is a duplication tower. It is also more economical because of little to none setup cost. That is why companies are able to have a very low minimum (such as 10 or 50) with duplication. You will get your products much quicker, usually within a few days time, but you do pay a higher per unit price for each disc.
Is duplication lower quality than replication?
The short answer is no. The quality of the products is only as good as the original master. What most people are concerned with is the compatibility of discs with DVD players. It is not the same as quality. Nowadays about 90-95% of players are compatible with CD-R/DVD-R, with the exception of Playstation and X-Box. Just remember, the key is to thoroughly test the original master, otherwise problems will still arise no matter which method you use.
Microsoft Excel 2007 Tutorial
Microsoft Excel 2007 Tutorial – document, simply click on the MS 2007 logo in the top left-hand corner [ ] and the menu bar that you see on your right here will drop down giving you various options, including saving.To get help in Excel 2007, look for the help icon [ ] in the top right-hand corner of the screen and click on it.You will be presented with a window that looks like the one here on the right.To access the slide master, go to the View tab and select “Slide Master”Also, when you have a blank slide (or parts of a blank slide), you can also click on options within these blank compartments to insert pictures. when you have a blank slide (or parts of a blank slide), you can also click on options w/nthese blank compartments to insert tables.
Get from here to download Microsoft Excel 2007 Tutorial
Wednesday, March 27, 2013
Using the Getting Things Done methodology in the LeaderTask organizer
GTD is an action management strategy and also a system of methods and techniques the purpose of which is to help a modern person complete more and get tired less. The GTD abbreviation stands for Getting Things Done which is the name of a book by an American business trainer David Allen.
The main principles of GTD with examples of how it can be done in LeaderTask:
1) Organizing information. All incoming information must be stored in one place. This way it is easier to view it and find what you need. And all information should be divided into actions, i.e. what you should do (tasks in LeaderTask), and reference information (notes in LeaderTask).
2) Grouping tasks by context. It is better to perform tasks that have the same context (place, person, event, ...) together (several at a time) even if they belong to different projects.
Examples:
context Bank: it is better to do all tasks related to the bank at once instead of doing only part of them belonging to some project/task.
context John Smith: when you see this person, it is better to solve all problems related to him at once instead of one task or just ignore altogether.
The only question is how to remember what should be done at the right time in the right place? LeaderTask is specifically designed to give answers to these question with one click. Examples: when you go the bank, you print a todo list with tasks filtered by the following criteria: "Bank: all tasks". When you accidentally see John Smith in a bus, you look at the todo list and see all tasks realted to him (besides, tasks will most probably be from different projects).
In other words, grouping tasks by context = doing relevant things right here right now.
* context is more often called kairos in terms of time mamagement.
3) Criteria for selecting tasks to do
1. By context (what is to be done in this place? with this person? in case of this event?)
2. By time (what is to be done at this time? and do I have time to do it?)
3. By effort (do I have energy to complete this task?)
4. By priorities (what is the most important thing to do?)
All criteria except for # 3 (since the computer cannot decide how you feel) are present in LeaderTask:
Context and time are implemented in "Categories", "Contacts", "Time periods (dates)", "Projects";
Priorities are implemented as priorities and the user can define his own set of priorities and group tasks using this set.
4) Natural planning model.
The model of planning a project proposed by David Allen:
1. Defining the purpose ("why") and principles of work.
2. Envisioning the desired outcome
3. Brainstorming the way how to achieve this outcome
4. Organizing work
5. Identifying next actions
Projects are represented as a separate section in LeaderTask. Project properties include its goals, the responsible person, its time frame, the "project completed" mark. All actions (tasks) by the project are kept within its context, i.e. displayed when it is active.
5) Weekly review.
The number of tasks is constantly increasing, ideas, thoughts, solutions keep coming to us all the time. There are useful and not very useful ones among them. For you not to get lost in heaps of your own plans, David Allen recommends that you do a review at least once a week - "Weekly review". This review will help you get rid of irrelevant tasks, make your goals clearer, evaluate how close you are to your goals, etc.
The main priority in LeaderTask is making it comfortable to view tasks. It is achieved with the help of "Filters", i.e. predefined sets of criteria tasks will be filtered by.
Sample filters:
"My today tasks", "Bank tasks","IMPORTANT", "URGENT", "Monthly sales", "Project XYZ in September", "Delegated tasks", "Topics for meeting on project N", "Overdue tasks", "Yearly goals", "Calls", "Yearly goals review" ...
Thus, LeaderTask is very conveneint if you use David Allens methodology - Getting Things Done!
Use LeaderTask - complete more, get tired less!!!
Download LeaderTask
http://www.leadertask.com/download/leader.exe
LeaderTask homepage
http://www.leadertask.com/
LeaderTask support forum
http://www.todoforum.com/
Read More..
The main principles of GTD with examples of how it can be done in LeaderTask:
1) Organizing information. All incoming information must be stored in one place. This way it is easier to view it and find what you need. And all information should be divided into actions, i.e. what you should do (tasks in LeaderTask), and reference information (notes in LeaderTask).
2) Grouping tasks by context. It is better to perform tasks that have the same context (place, person, event, ...) together (several at a time) even if they belong to different projects.
Examples:
context Bank: it is better to do all tasks related to the bank at once instead of doing only part of them belonging to some project/task.
context John Smith: when you see this person, it is better to solve all problems related to him at once instead of one task or just ignore altogether.
The only question is how to remember what should be done at the right time in the right place? LeaderTask is specifically designed to give answers to these question with one click. Examples: when you go the bank, you print a todo list with tasks filtered by the following criteria: "Bank: all tasks". When you accidentally see John Smith in a bus, you look at the todo list and see all tasks realted to him (besides, tasks will most probably be from different projects).
In other words, grouping tasks by context = doing relevant things right here right now.
* context is more often called kairos in terms of time mamagement.
3) Criteria for selecting tasks to do
1. By context (what is to be done in this place? with this person? in case of this event?)
2. By time (what is to be done at this time? and do I have time to do it?)
3. By effort (do I have energy to complete this task?)
4. By priorities (what is the most important thing to do?)
All criteria except for # 3 (since the computer cannot decide how you feel) are present in LeaderTask:
Context and time are implemented in "Categories", "Contacts", "Time periods (dates)", "Projects";
Priorities are implemented as priorities and the user can define his own set of priorities and group tasks using this set.
4) Natural planning model.
The model of planning a project proposed by David Allen:
1. Defining the purpose ("why") and principles of work.
2. Envisioning the desired outcome
3. Brainstorming the way how to achieve this outcome
4. Organizing work
5. Identifying next actions
Projects are represented as a separate section in LeaderTask. Project properties include its goals, the responsible person, its time frame, the "project completed" mark. All actions (tasks) by the project are kept within its context, i.e. displayed when it is active.
5) Weekly review.
The number of tasks is constantly increasing, ideas, thoughts, solutions keep coming to us all the time. There are useful and not very useful ones among them. For you not to get lost in heaps of your own plans, David Allen recommends that you do a review at least once a week - "Weekly review". This review will help you get rid of irrelevant tasks, make your goals clearer, evaluate how close you are to your goals, etc.
The main priority in LeaderTask is making it comfortable to view tasks. It is achieved with the help of "Filters", i.e. predefined sets of criteria tasks will be filtered by.
Sample filters:
"My today tasks", "Bank tasks","IMPORTANT", "URGENT", "Monthly sales", "Project XYZ in September", "Delegated tasks", "Topics for meeting on project N", "Overdue tasks", "Yearly goals", "Calls", "Yearly goals review" ...
Thus, LeaderTask is very conveneint if you use David Allens methodology - Getting Things Done!
Use LeaderTask - complete more, get tired less!!!
Download LeaderTask
http://www.leadertask.com/download/leader.exe
LeaderTask homepage
http://www.leadertask.com/
LeaderTask support forum
http://www.todoforum.com/
Labels:
done,
getting,
in,
leadertask,
methodology,
organizer,
the,
things,
using
5 Top YouTube Apps for Windows 8
5 Top YouTube Apps for Windows 8:
Windows 8 comes with many new features and one of the major one is the new Windows Store which allows you to install app on your Windows 8 desktops and tablets from the app store. YouTube being the most popular video sharing service, you might obviously want to use it on your tablets, but Google has already mentioned that it wont be developing any Google apps for Windows 8 as of now.
But like any other platform, there are many alternative apps developed by other software developers, some of them providing better features than the official app (on other platforms). In this article we will cover the best third party YouTube players and downloaders available for Windows 8.


There are many more apps in the Windows store which allows you to search and watch YouTube videos also with the option to download them.
Via Nirmaltv
Windows 8 comes with many new features and one of the major one is the new Windows Store which allows you to install app on your Windows 8 desktops and tablets from the app store. YouTube being the most popular video sharing service, you might obviously want to use it on your tablets, but Google has already mentioned that it wont be developing any Google apps for Windows 8 as of now.
But like any other platform, there are many alternative apps developed by other software developers, some of them providing better features than the official app (on other platforms). In this article we will cover the best third party YouTube players and downloaders available for Windows 8.
Best YouTube apps for Windows 8:
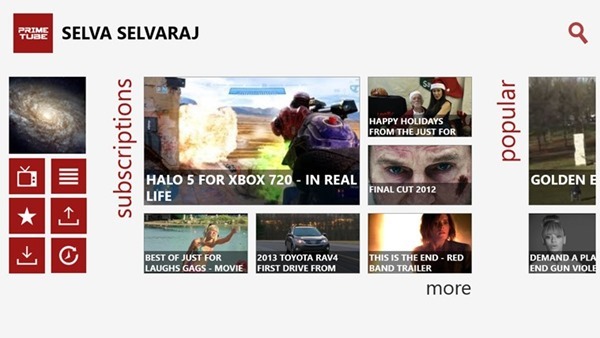
1. PrimeTube:
PrimeTube is the most elegant way to access YouTube from your Windows 8 tablet, desktop, and laptop. The app is created by the developers of the acclaimed Windows Phone PrimeTube app. Uniquely designed ,the app provides you an immersive experience to search, watch and manage your YouTube videos. Record and Upload videos to YouTube in just a few clicks. You can also manage subscriptions, favorites, playlists and watch later videos. We have covered this app on this blog.
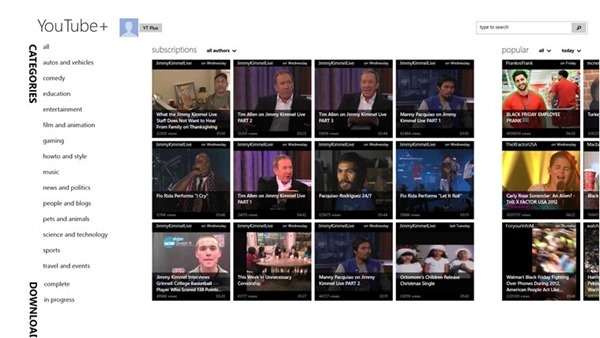
2. YouTube+:
YouTube+ is the top rated YouTube application for Windows 8. This is a paid app with a free trial version available. The feature rich client allows you to view common video feeds like popular, trending and most recent. You can also a select a region to view region specific results. You can search for YouTube videos and filter based on category and relevance.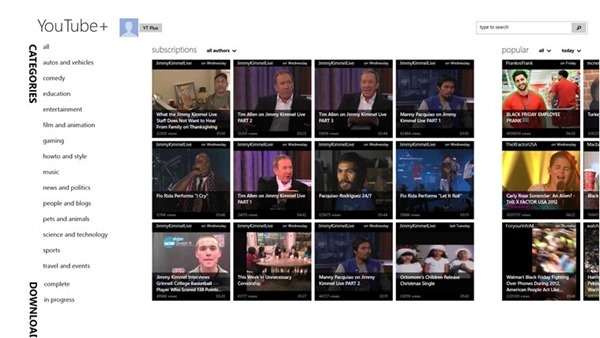
3. Andatube:
ANDATUBE is a Free limited time YouTube client specialized in Music and Movies, where you can browse, stream,download your favorite videos with easily. One of the best feature of this app is that it shows lyrics of popular videos while playing them. More details available here.
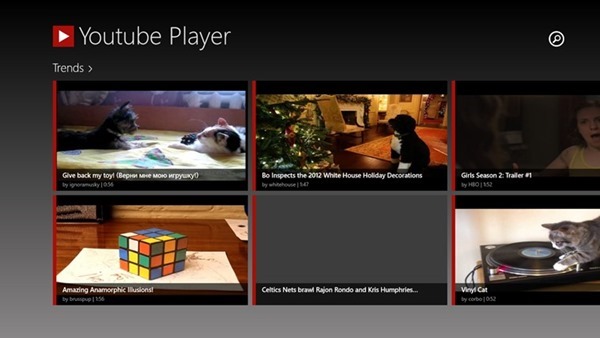
4. YouTube Player:
With the YouTube Player for Windows 8 you can search, watch a stream, share videos and access your personal content from YouTube. Everything included in the great user interface of Windows 8. More details here.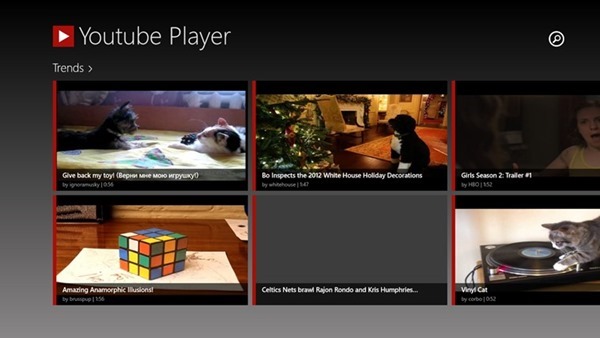
5. Your Tube 8:
Your Tube 8 is a simple and fast YouTube client Windows 8 app which allows you to search for YouTube videos and view them from your Windows 8 device. The UI is attractive and the navigation system is simple. Search can be performed by keyword (in English), category or type or by any combination between them.
There are many more apps in the Windows store which allows you to search and watch YouTube videos also with the option to download them.
Via Nirmaltv
Quick Microsoft Access 2003 Tutorial
This tutorial is intended for computer science students who need a quick introduction to Microsoft Access, but it will be useful to anyone needing such an introduction. To get the full benefit of this tutorial, you will need a computer running one of Microsoft Windows 95 or higher, Microsoft NT 4.0 or higher, or Microsoft Windows 2000/XP. You will also need to have a copy of Microsoft Access 2003 installed. 2 First, a few words about what Microsoft Access 2003 is and isn’t. People who don’t really understand what a relational database system is, and some people who don’t actually understand what Access 2003 is, will tell you that Microsoft Access is not a fully relationaldatabase system. In the database world, not being fully relational is very bad. Don’t worry, the people who tell you that are like the people who try to tell you that linux is not a 32 bit operating system. Access 2003, and its predecessors Access 95, 97 and 02, are excellent fully relationaldatabase systems.
Spyware Its Hidden Agenda
We have all heard about spyware. Spyware is regularly featured in various news media and is a topic of much discussion in computer circles. The reason for this is the constant bombardment of spyware related material, that infiltrates computer systems. Spyware has a hidden agenda.
The Internet is loaded with information on every conceivable subject. There are ebooks, software, photos, file sharing and a host of giveaways that are very enticing to computer users, especially those that have a hobby or special interest. The desire to take advantage of the vast internet resources and to download files or to share files, photos, software etc. is growing at a very fast pace. Advertisers and marketing specialists are aware of this trend and they focus their attention on providing online surfers with software, ebooks and other giveaways that cater to individual interests. These "Giveaways" are the "Passage way" used by promotional companies to get entry into the internet users computer.
Spyware "Piggybacks" on very innocent and legitimate looking file downloads. It can be likened to a passport that allows a person to enter a country, only in this case it is to enter an individuals computer, without the user fully understanding the implications of such file downloads. <
Spyware introduced into a computer system loves the environment. It has gained entrance into the system and feeds on the information the system contains. Its prying eyes feasts on the "Goings on" and learns all of the habits, interests, chats, discussions and shares this information with its buddies on the other side of the internet line. Who are its buddies? You guessed right, it is the promotional companies. This approach enables promotional companies to become fully aware of peoples interests, needs and desires. In turn, they will direct their wares to the individuals whose system was infiltrated by spyware.
People treasure privacy, be it at home or on the internet. It is easy to enjoy privacy at home, it is not as easy to enjoy computer privacy. A Loss of privacy on the internet can bring about numerous hardships, financial losses and of course can lead to identity theft.
People linked to the internet need to install spyware removal software. Spyware software will enable a scan, of all the files on ones computer and allow for the removal, of unwanted files, that pose a risk to privacy.
You can get a Free Spyware Scanner at http://www.DeleteSpyware.net
Read More..
The Internet is loaded with information on every conceivable subject. There are ebooks, software, photos, file sharing and a host of giveaways that are very enticing to computer users, especially those that have a hobby or special interest. The desire to take advantage of the vast internet resources and to download files or to share files, photos, software etc. is growing at a very fast pace. Advertisers and marketing specialists are aware of this trend and they focus their attention on providing online surfers with software, ebooks and other giveaways that cater to individual interests. These "Giveaways" are the "Passage way" used by promotional companies to get entry into the internet users computer.
Spyware "Piggybacks" on very innocent and legitimate looking file downloads. It can be likened to a passport that allows a person to enter a country, only in this case it is to enter an individuals computer, without the user fully understanding the implications of such file downloads. <
Spyware introduced into a computer system loves the environment. It has gained entrance into the system and feeds on the information the system contains. Its prying eyes feasts on the "Goings on" and learns all of the habits, interests, chats, discussions and shares this information with its buddies on the other side of the internet line. Who are its buddies? You guessed right, it is the promotional companies. This approach enables promotional companies to become fully aware of peoples interests, needs and desires. In turn, they will direct their wares to the individuals whose system was infiltrated by spyware.
People treasure privacy, be it at home or on the internet. It is easy to enjoy privacy at home, it is not as easy to enjoy computer privacy. A Loss of privacy on the internet can bring about numerous hardships, financial losses and of course can lead to identity theft.
People linked to the internet need to install spyware removal software. Spyware software will enable a scan, of all the files on ones computer and allow for the removal, of unwanted files, that pose a risk to privacy.
You can get a Free Spyware Scanner at http://www.DeleteSpyware.net
resonicplayer Is A Minimal Music Player With A Built In File Browser
resonicplayer Is A Minimal Music Player With A Built-In File Browser:
Read More..
Having a playlist of your favorite music playing in the background while working on the computer is a regular habit of a lot of computer users. However, most major media players such as Windows Media Player and several third-party alternatives have flashy interfaces and too many options that can easily distract a person from their actual work. Moreover, having so many options is useless for someone who just wants to listen to some music in the background. Some days ago, we covered the newly released GOM Audio by the developers of GOM Player that boasted a compact design and impressive features. However, if you are looking for a lightweight music player that does not put much stress on the system, does not have a lot of flashy options, and offers a simply way to play music from your audio collection, try resonicplayer. It is an audio player currently available only for Windows that provides you with a simple and user-friendly interface. Moreover, you can set a timer on the application to perform a number of operations after a certain time, making it useful for people who like to go to sleep while listening to music.
As stated earlier, the application sports a very simple interface. At the top, you’ll see the playback controls, as well as the selected visualization. The left side has the Browser pane that allows you to navigate through your drives and libraries to look for the folder containing your favorite music. When a music folder is selected, all its files are listed in the right side. Each file is displayed along with its name, size, artist, title, year of release and length. Click any song in the right pane to instantly start playing it. The playback controls allow you to play, pause, stop, move to next or previous track, and choose repeat and shuffle options.

The Menu button lets you select the Visualization, Playback options and a sleep timer. You can choose to play the songs sequentially, shuffle them, or stop playback after the current song.

The Sleep Timer is a really good feature and lets you start playback before going to sleep without worrying about the PC staying on for the whole night. You can choose to Sleep, Hibernate, Power off, Log off, Lock or just stop the audio playback after an interval of your choice, or from one of the provided options.

resonicplayer is available in both portable and installable versions, and works on 32-bit and 64-bit variants of Windows XP, Windows Vista, Windows 7 and Windows 8.
Download resonicplayer
As stated earlier, the application sports a very simple interface. At the top, you’ll see the playback controls, as well as the selected visualization. The left side has the Browser pane that allows you to navigate through your drives and libraries to look for the folder containing your favorite music. When a music folder is selected, all its files are listed in the right side. Each file is displayed along with its name, size, artist, title, year of release and length. Click any song in the right pane to instantly start playing it. The playback controls allow you to play, pause, stop, move to next or previous track, and choose repeat and shuffle options.

The Menu button lets you select the Visualization, Playback options and a sleep timer. You can choose to play the songs sequentially, shuffle them, or stop playback after the current song.

The Sleep Timer is a really good feature and lets you start playback before going to sleep without worrying about the PC staying on for the whole night. You can choose to Sleep, Hibernate, Power off, Log off, Lock or just stop the audio playback after an interval of your choice, or from one of the provided options.

resonicplayer is available in both portable and installable versions, and works on 32-bit and 64-bit variants of Windows XP, Windows Vista, Windows 7 and Windows 8.
Download resonicplayer
4 Useful Websites To Help You Pronounce Names Correctly

As a blogger I have to answer many questions to readers from across the world. Luckily, I converse with them either via emails or on post threads. Lucky because, if you are talking to someone from a different country you might not be able to pronounce names correctly.
Indeed, it is not the easiest thing to do even in your own land. You might come across names that are uncommon and unheard of, and which you have a hard time pronouncing the right way.
To help you feel easy in such awkward situations of not being able to pronounce names correctly, we have compiled a list of 4 websites. These sites could come in handy, especially when you travel abroad. Let us check them out.

The results will show the name you were searching for (and a few more related names) under different categories. Here’s an example we tried.

If you don’t find the name you are searching for then you could request to add that name by filling a simple form.

You can search a name, browse the list and check pronunciation of any name. If you do not find one you may request pronunciation of a name or submit one by uploading wav/mp3 files.
Sometimes it is not just about names of people. You may also want to learn about names of places and various other things. If it is so, Inogolo might help.

When you search for names you will be guided with results in both phonetic and audio, both in English language. The good thing is that it also shows the origin of the name. Here’s an example.

This website is useful for both English and non English speakers because it displays phonetic pronunciations using respelled transcription having no special characters, signs or symbols.
Cool Tip: There are a number of pronunciation guides available on Inogolo. Check them out here. You may find something of your interest.
If you look at the home page you will be able to see various categories like Golf, Tennis, etc. You can click on them to see who is listed on the website. Or you can also search for your favorite personality by using the search box.

Tell us about you favorite choice. If you are aware of something different, do let us know.
To help you feel easy in such awkward situations of not being able to pronounce names correctly, we have compiled a list of 4 websites. These sites could come in handy, especially when you travel abroad. Let us check them out.
Hear Names
Hear Names, as the name suggests, lets you hear the correct pronunciation of difficult names. All you need to do is type the name in the search box at the home page and press Enter.
The results will show the name you were searching for (and a few more related names) under different categories. Here’s an example we tried.

If you don’t find the name you are searching for then you could request to add that name by filling a simple form.
Pronounce Names
Pronounce Names is similar to Hear Names. It has a huge collection of names and their pronunciations. As a user you would see the below interface on its home page.
You can search a name, browse the list and check pronunciation of any name. If you do not find one you may request pronunciation of a name or submit one by uploading wav/mp3 files.
Inogolo
Sometimes it is not just about names of people. You may also want to learn about names of places and various other things. If it is so, Inogolo might help.

When you search for names you will be guided with results in both phonetic and audio, both in English language. The good thing is that it also shows the origin of the name. Here’s an example.

This website is useful for both English and non English speakers because it displays phonetic pronunciations using respelled transcription having no special characters, signs or symbols.
Cool Tip: There are a number of pronunciation guides available on Inogolo. Check them out here. You may find something of your interest.
The Name Engine
The Name Engine is a website dedicated to correct name pronunciation of famous personalities such as athletes, entertainers, politicians, news makers etc.If you look at the home page you will be able to see various categories like Golf, Tennis, etc. You can click on them to see who is listed on the website. Or you can also search for your favorite personality by using the search box.

Conclusion
Go ahead and try out a few names. I am sure you will discover many new pronunciations and you will also discover that you were treating many of them wrongly. And, if I am correct you will definitely bookmark these websites.Tell us about you favorite choice. If you are aware of something different, do let us know.
Tuesday, March 26, 2013
AntennaPod Is A Feature Rich Podcast Vodcast Manager For Android
AntennaPod Is A Feature-Rich Podcast & Vodcast Manager For Android:

Over the past few months, quality podcast management apps for Android are slowly but surely starting to show up in the Play Store. Just recently, we saw a very promising Holo-themed podcast app Volksempfanger that supported some nifty features such as auto-downloading of new episodes, downloading over Wi-Fi or in charging mode only, and plenty more. Today, we’ll take a look at AntennaPod – a full-featured podcast and vodcast manager for Android. Besides sporting a gorgeous Holo-themed UI with multiple shades, AntennaPod boasts quite a few handy tools that are hard to find in a single package, and that too for free!


Before we jump to the features list of AntennaPod, we’d like to mention here that the app is currently in beta, and compatible with Android 2.3.3 Gingerbread or higher devices. That said, here is the list of features AntennaPod currently offers:








Currently being in beta, the app is understandably carrying a few trivial bugs such as an odd force close instance, inability to download feeds occasionally, and a slightly unhelpful search engine. Besides fixing these odd glitches, the developers can introduce several additional features. We would love to see the option to sync personalized content across devices. The widgets can be beefed up with slightly better controls and aesthetics. Similarly, the download manager of the app can be enhanced by adding the option to download content in charging mode only. Last but not the least, the option to manage feeds and underlying content in bulk, if added, will prove to be a huge bonus.


That being said, even in its current form, AntennaPod is beefy enough to grab the attention of avid podcast and vodcast fans with Android devices.
Download AntennaPod For Android
Via Addictivetips


Before we jump to the features list of AntennaPod, we’d like to mention here that the app is currently in beta, and compatible with Android 2.3.3 Gingerbread or higher devices. That said, here is the list of features AntennaPod currently offers:
- Multilingual support (currently available in English, German & Russian).
- Downloading & streaming of high quality podcasts and vodcasts.
- Separate columns for your feeds, new content and queued items.
- Universal search tool to easily look for content.
- Light and dark themes.
- Option to subscribe to new feeds by custom URLs.
- Miro Guide integration to subscribe to interesting content from an extensive category-based repository.
- OPML support to allow users to move (import & export) their podcasts from one podcatcher to another.



- Option to share URLs and visit websites of select sources.
- Support for RSS and Atom feeds.
- Detailed logging of playback history and download tasks.
- Support for MP3, simple and VorbisComment chapters.
- One-tap refresh of items listed under select subscriptions.
- Episode-by-episode listing of content featured under each subscription, with indication about the last played item via a color-coded bar.
- Complete overview of feeds and brief information regarding each episode.
- Polished podcast player UI supplemented with background playback support, podcast cover, shownotes, and basic playback controls.


- Option to set custom sleep timer (in seconds, minutes or hours) for podcasts and vodcasts to automatically quit the app after a specified duration.
- Notification bar alerts for current playback and download status.
- Home screen widget and lockscreen controls to play/pause podcasts conveniently.
- Advanced options such as pause upon headset disconnection, continuous playback of episodes, and auto-deletion of episodes after playback is completed.

- Custom update interval to refresh the feeds.
- Option to download items over cellular data connection.
- Auto-queuing of episodes when set to download.
- Complete Flattr integration.


Currently being in beta, the app is understandably carrying a few trivial bugs such as an odd force close instance, inability to download feeds occasionally, and a slightly unhelpful search engine. Besides fixing these odd glitches, the developers can introduce several additional features. We would love to see the option to sync personalized content across devices. The widgets can be beefed up with slightly better controls and aesthetics. Similarly, the download manager of the app can be enhanced by adding the option to download content in charging mode only. Last but not the least, the option to manage feeds and underlying content in bulk, if added, will prove to be a huge bonus.


That being said, even in its current form, AntennaPod is beefy enough to grab the attention of avid podcast and vodcast fans with Android devices.
Download AntennaPod For Android
Via Addictivetips
Subscribe to:
Comments (Atom)
